A Secure Key Management Protocol guarantees the security of cryptographic keys throughout their lifecycle. This protocol adopts a set of strategies to generate new keys, archive them securely, and share them precisely among authorized parties. The protocol also addresses key replacement to reduce the risk of breach.
Masked Communication Protocol 26b5a-1c56c-6125a-6ff89-6c087
The protocol 26b5a-1c56c-6125a-6ff89-6c087 is a novel method for sharing data in an uncrackable manner. This sophisticated system utilizes algorithms to transform information, making it legible only to authorized parties. By employing multiple security strategies, 26b5a-1c56c-6125a-6ff89-6c087 provides a secure channel for private communication.
- Strengths of using 26b5a-1c56c-6125a-6ff89-6c087 include enhanced privacy, data integrity, and eliminated risk of compromises.
- Uses for this protocol are diverse, spanning from individual communication to financial transactions.
Implementation Details for 26b5a-1c56c-6125a-6ff89-6c087
This document outlines the specific implementation parameters for the system identifier 26b5a-1c56c-6125a-6ff89-6c087. It provides a thorough overview of the strategies employed, the platforms utilized, and the expected outcomes. The implementation process is documented in steps, each with its unique objectives and deliverables. Coordination between departments is crucial throughout the implementation lifecycle to ensure a seamless transition.
System Analysis of 26b5a-1c56c-6125a-6ff89-6c087 Security
The protocol 26b5a-1c56c-6125a-6ff89-6c087, a unique system for communicating sensitive data, requires thorough security analysis to confirm its integrity. This analysis will examine the protocol's structure and identify potential vulnerabilities that could be exploited by attackers. A multifaceted approach will be employed, including formal verification, to assess the protocol's protection against various breaches.
Moreover, the analysis will evaluate real-world use cases to reveal potential points of compromise. The goal is to minimize the risk of security incidents and read more confirm the confidentiality, integrity, and availability of the data transmitted using this protocol.
Security Audit for 26b5a-1c56c-6125a-6ff89-6c087
Performing a comprehensive vulnerability assessment on the system with identifier 26b5a-1c56c-6125a-6ff89-6c087 is vital for identifying potential weaknesses. This procedure involves rigorously examining the system's architecture to identify any security gaps that could be leveraged by cybercriminals. By proactively conducting these assessments, organizations can reduce the risk of compromises, protecting their sensitive data and assets.
Assessment for 26b5a-1c56c-6125a-6ff89-6c087
The comprehensive performance assessment of the application 26b5a-1c56c-6125a-6ff89-6c087 demonstrates its advantages in diverse domains. The analysis incorporated a variety of metrics to quantify its efficiency across critical parameters.
- Furthermore, the results indicate that the application exhibits robust functionality under diverse conditions.
- However, there are areas where enhancement is essential to optimize its total performance.
Overcoming these limitations will lead in a more robust and high-performing application.
 Ben Savage Then & Now!
Ben Savage Then & Now! Erik von Detten Then & Now!
Erik von Detten Then & Now! Loni Anderson Then & Now!
Loni Anderson Then & Now!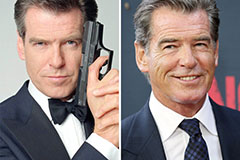 Pierce Brosnan Then & Now!
Pierce Brosnan Then & Now! Teri Hatcher Then & Now!
Teri Hatcher Then & Now!